A computer virus is a form of malware designed to replicate and spread among devices, typically without the user’s knowledge. It operates in a manner similar to a biological virus by attaching itself to legitimate software, files, or the boot sector of a hard drive in order to spread. Once triggered, a computer virus can carry out various harmful actions ranging from minor pranks to severe offenses, such as stealing data, disrupting system functions, and causing complete system failure. It is crucial for both individuals and organizations to understand how computer viruses work in order to enhance their cyber-security practices and protect the security of their digital systems.
History of computer viruses
The history of computer viruses demonstrates the evolving challenges of cybersecurity. The concept was initially proposed by John von Neumann in 1949, but it was not until the Creeper virus in 1971 that a practical example of self-replicating software was observed. The term “virus” was coined in 1983 by Fred Cohen, and the first significant PC virus to spread in the wild was the Brain virus, developed in 1986 by the Farooq Alvi brothers. In the 1980s, viruses spread through floppy disks, while the 1990s saw a rapid increase in online proliferation with the rise of the internet, resulting in infamous attacks such as the Melissa virus and the ILOVEYOU worm. These incidents not only caused substantial financial harm but also exposed vulnerabilities in systems like Windows 95, prompting the growth of the antivirus software industry to combat the growing sophistication of malware and safeguard digital infrastructure and users.
Types of Computer Viruses
In cybersecurity, a variety of computer viruses pose distinct threats, each requiring specific defense strategies. Boot Sector Viruses compromise the master boot record and often necessitate a full system format for removal. Direct Action and File Infector Viruses attach to and replicate through files, with the former easily removable by antivirus software, while the latter disrupts system performance upon file execution. Resident Viruses reside in system memory, acting independently of host files and complicating detection and removal. Polymorphic Viruses evade signature-based detection by altering their code with each infection. Macro Viruses use macro languages of applications to spread through document sharing. Overwriting Viruses replace original file content with malicious code, and Multipartite Viruses infect both files and boot sectors. Network Viruses spread across networks via shared resources. Web Scripting Viruses exploit web page code to infect systems upon user interaction with compromised web content. Awareness and proactive measures are essential to prevent significant data loss and system damage caused by these viruses.
- File infectors
- Macro viruses
- Boot sector viruses
- Polymorphic viruses
- Stealth viruses
- Resident versus non-resident viruses
- Multipartite Virus
- Overwrite Virus
- File Infector Virus
- Spacefiller Virus
- Web Scripting Virus
- Browser Hijacker
- Direct Action Virus
How Computer Viruses Spread
Computer viruses are malicious programs created to infiltrate and harm computers, often spreading quickly through different digital channels. They can be transmitted through email attachments, hidden in downloadable files, or even spread through infected external media such as USB drives. Understanding how they are transmitted is essential for effective prevention and protection.
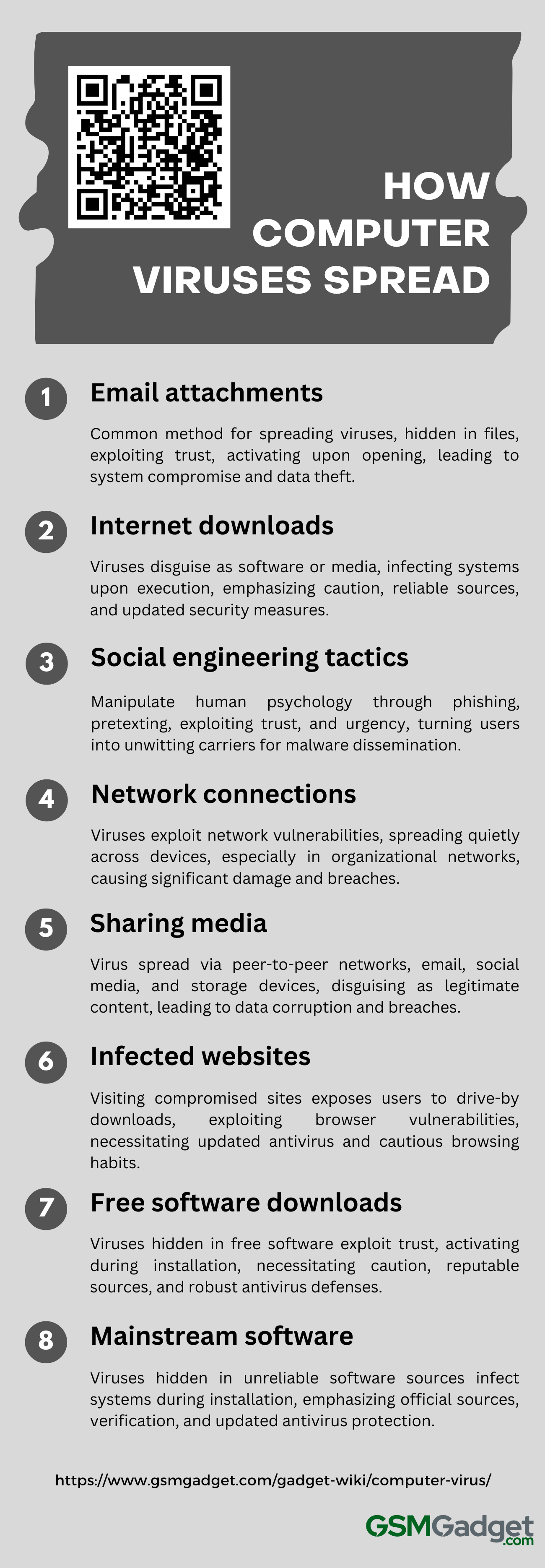
1. Email attachments
Email attachments are a common method used by cybercriminals to distribute computer viruses. Malware is often hidden within seemingly harmless files, such as documents or images, in order to deceive users. These attachments can automatically activate when opened and may appear to come from a trusted source, using social engineering tactics to manipulate users into taking quick actions. The activation of a virus can result in system compromise, data theft, and further spread as it replicates and spreads through the victim’s contacts. To protect against this threat, it is important to regularly update antivirus software, exercise caution with unexpected emails, and avoid opening attachments from suspicious senders. Organizations can enhance their defenses by implementing email filters that can detect and isolate potential threats, reducing the risk of virus propagation through email attachments.
2. Internet downloads
Computer viruses spread rapidly through internet downloads, often disguising themselves as harmless software, updates, or media files from questionable sources. These malicious programs can trick users, infiltrating systems upon execution and causing replication, data corruption, or more serious consequences. The risk increases when users overlook security measures, such as using outdated antivirus software or downloading from untrustworthy websites. To address this issue, it is crucial to only download from reliable sources, maintain up-to-date security software, and regularly scan systems for potential threats. This proactive approach is essential for protecting against the harmful effects of computer viruses transmitted through internet downloads.
3. Social engineering tactics
Social engineering tactics are a primary method through which computer viruses spread, utilizing human psychology to breach security rather than exploiting technical vulnerabilities. Cybercriminals employ advanced techniques such as phishing, pretexting, baiting, and quid pro quo to trick individuals into engaging in actions like clicking on malicious links, downloading compromised attachments, or disclosing confidential information. These strategies are alarmingly successful because they exploit inherent human characteristics such as trust, the inclination to assist others, and the tendency to react promptly to perceived emergencies. By exploiting these emotions, attackers can transform unsuspecting users into unwitting carriers for malware dissemination throughout networks and systems. The efficacy of social engineering highlights the crucial necessity for increased cybersecurity awareness and continual vigilance to protect against these deceitful and manipulative dangers.
4. Network connections
In the technology-focused field of cybersecurity, it is crucial to understand how computer viruses use network connections to spread. These viruses can quickly infect multiple devices by exploiting vulnerabilities in network protocols, hitching a ride on file transfers, or disguising themselves within email attachments. Once they gain access to a network, they replicate and spread quietly, often taking advantage of weak security measures such as easily guessed passwords or outdated software to move deeper into the system. The risk increases in organizational networks where many computers are connected, as a single infected device can trigger a chain reaction, spreading across shared resources and causing significant damage, data breaches, and operational disruptions before being detected. The very interconnectedness that is meant to streamline workflow becomes the pathway for these viruses to rapidly and stealthily multiply.
5. Sharing music, files, or photos with other users
The sharing of music, files, or photos among users can inadvertently facilitate the spread of computer viruses, particularly through peer-to-peer networks, email attachments, social media platforms, or removable storage devices. Malicious code is often embedded in these files, masquerading as legitimate content. When users download or open these infected files, the virus is activated, leading to replication and further distribution of the virus. This can result in potential harm such as data corruption, unauthorized access to sensitive information, or system failures. To minimize these risks, users should utilize robust antivirus software, keep their systems up to date, and remain vigilant when downloading or sharing files, even from seemingly trustworthy sources or popular websites.
6. Visiting an infected website
When a user visits a compromised website, they may unknowingly be exposed to malicious code that exploits vulnerabilities in their browser or its plugins, resulting in the silent download and execution of a computer virus. This code, often hidden in advertisements, downloadable files, or even standard website features, can initiate drive-by downloads that do not require user interaction. Exploit kits target these security gaps, sometimes redirecting to other pages hosting the malware, which can replicate, steal data, or turn the computer into part of a botnet. Even reputable websites can be temporarily compromised, posing risks to even the most cautious users. Therefore, maintaining updated antivirus software and being vigilant about the websites one visits are essential practices to safeguard against such threats.
7. Downloading free games, toolbars, media players and other system utilities
Computer viruses often exploit the allure of free software, such as games, toolbars, media players, and system utilities, to infiltrate and harm users’ systems. These downloads, though appearing harmless, may contain malicious code that activates upon installation, replicates itself, modifies system settings, and potentially takes control of browser sessions. Cybercriminals cleverly bundle these viruses with popular software, taking advantage of users’ trust. To protect against these threats, it is crucial to obtain software from reputable sources, carefully review installation processes for hidden extras, and maintain robust antivirus defenses. This vigilance helps safeguard system integrity and personal data from the deceptive nature of free, yet potentially dangerous, software downloads.
8. Installing mainstream software applications
The spread of computer viruses can occur during the installation of mainstream software applications if users are not vigilant. Malicious code can be hidden within software obtained from unreliable sources, such as peer-to-peer networks or counterfeit websites that imitate official ones. These viruses may activate during software installation, especially with free or trial versions, taking advantage of the user’s trust in the software’s legitimate appearance. To prevent such infections, it is crucial to download applications only from official vendor sites or authorized distributors, verify the integrity of downloads using checksums or digital signatures, and utilize updated antivirus programs to scan for threats during the installation process. This approach helps protect systems against deceptive practices that enable viruses to infiltrate through seemingly trustworthy software.
Symptoms of a Virus Infection
A virus infection can be as debilitating to a computer system as a physical ailment is to the human body. Recognizing the early signs of such an infection is crucial for maintaining the health and security of your computer. Below is a list of common symptoms that may indicate your system has been compromised by a virus.
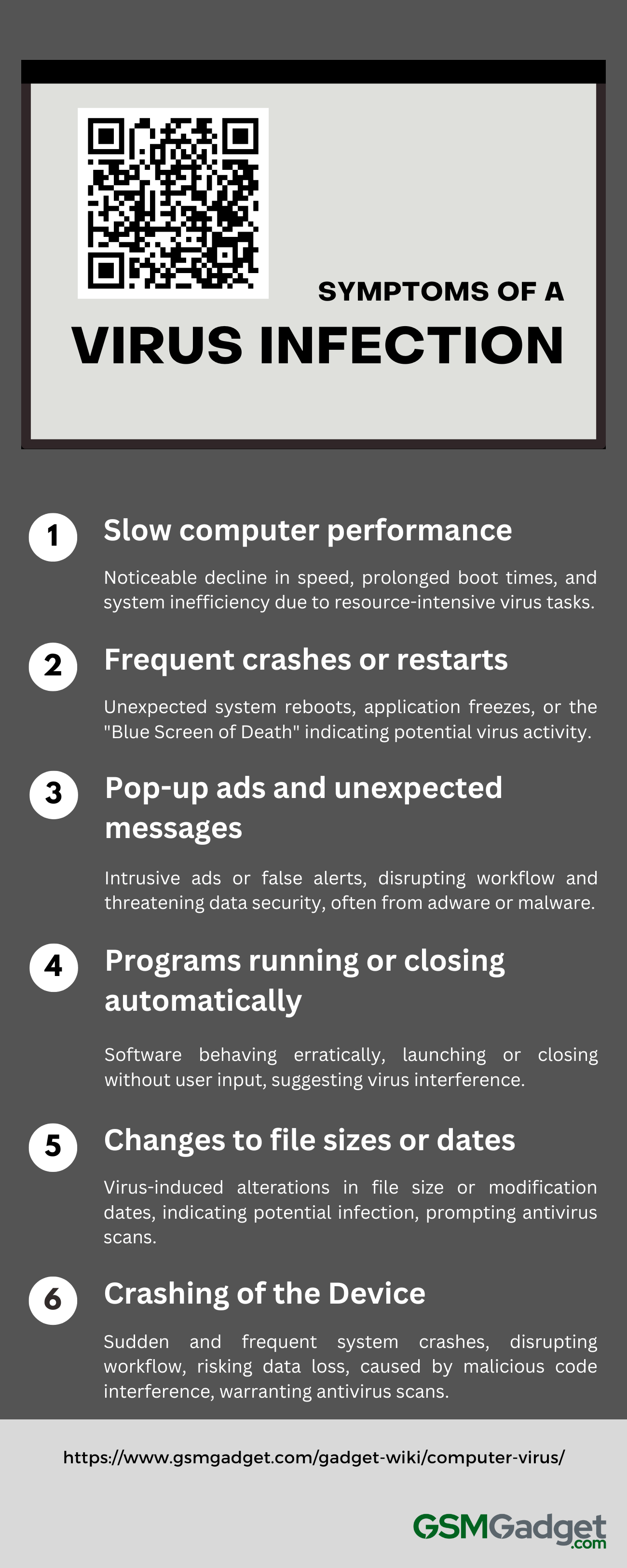
1. Slow computer performance
A virus infection frequently results in a noticeable decline in computer performance, marked by prolonged boot times, slow responsiveness to commands, and a overall decrease in system efficiency. These performance issues occur as the virus carries out resource-intensive background tasks, monopolizing CPU and memory resources, leading to potential system instability, data security risks, and frequent application crashes. To address these issues and restore normal operation, it is crucial to perform a comprehensive antivirus scan to identify and remove the virus promptly.
2. Frequent crashes or restarts
Frequent crashes or unexpected system restarts are telltale signs of a potential virus infection in the computing world. Such disruptive behavior can present as application freezes, the “Blue Screen of Death” on Windows, or spontaneous reboots, all of which can disrupt workflow and risk data loss. These issues often indicate that a virus is tampering with system processes or trying to avoid detection. To address this, users should promptly perform a security scan with trusted antivirus software and apply all necessary system updates and patches to close off any vulnerabilities that could be exploited by the virus.
3. Pop-up ads and unexpected messages
In the field of cyber-security, persistent pop-up advertisements and unexpected messages are warning signs of a potential computer virus infection. These pop-ups can appear as intrusive ads or false system alerts, designed to deceive users into downloading more malware or revealing private information. They often appear without user interaction, disrupting workflow and posing a threat to data security and privacy. Some messages may briefly flash on the screen, a common tactic used by adware to distribute misleading content through the system’s notification service. It is important to approach these pop-ups with skepticism and caution, as interacting with them can worsen the situation by further compromising system security and exposing personal data. To reduce these risks and restore the health of your device, it is recommended to run antivirus scans and perform system cleanups to prevent additional intrusions.
4. Programs running or closing automatically
In the context of cyber-security, a significant symptom of a potential virus infection is the unexpected and erratic behavior of software programs, which may start or stop without the user’s command. Applications might launch on their own, hinting at a virus trying to propagate or undermine the system’s security, or they could shut down suddenly to avoid detection and interrupt operations. These anomalies are serious indicators of trouble, often leading to data loss, compromised system stability, and the risk of the virus spreading. It is crucial for users who notice such behaviors to promptly run a comprehensive antivirus scan and possibly seek expert IT assistance to address the infection and fortify their system against subsequent attacks.
5. Changes to file sizes or dates
In the field of digital security, a subtle indicator of a virus infection is the unexpected change in file sizes or modification dates. Malicious software can manipulate files by adding code to executable files or corrupting data, resulting in changes in file size. Viruses can also change file timestamps to conceal their actions or trigger specific operations at set times. It is important for users to be vigilant of files that suddenly increase in size or have modification dates that do not align with their typical usage patterns. These abnormalities can serve as early warning signs, prompting a thorough system scan using updated antivirus software to detect and eliminate potential threats. Monitoring for such irregularities is a crucial practice in the early identification and prevention of virus infections.
6. Crashing of the Device
Frequent and unexpected system crashes are a characteristic symptom of a virus infection in devices, often leading to sudden reboots, the “blue screen of death” on Windows, or kernel panics on Macs. These crashes disrupt workflow and pose a risk of data loss, typically caused by malicious code that disrupts system processes or corrupts files, resulting in resource overload or irreconcilable conflicts. Additional signs may include slow performance, unresponsive applications, and automatic shutdowns. To prevent further damage and restore device functionality, users should promptly conduct antivirus scans and seek assistance from IT professionals if they notice such instability.
Prevention and Protection Strategies
In the field of technical writing, it is crucial to effectively communicate clear and actionable information, especially when discussing important topics such as prevention and protection. The following list outlines a set of strategic measures aimed at reducing risks and protecting against potential threats.
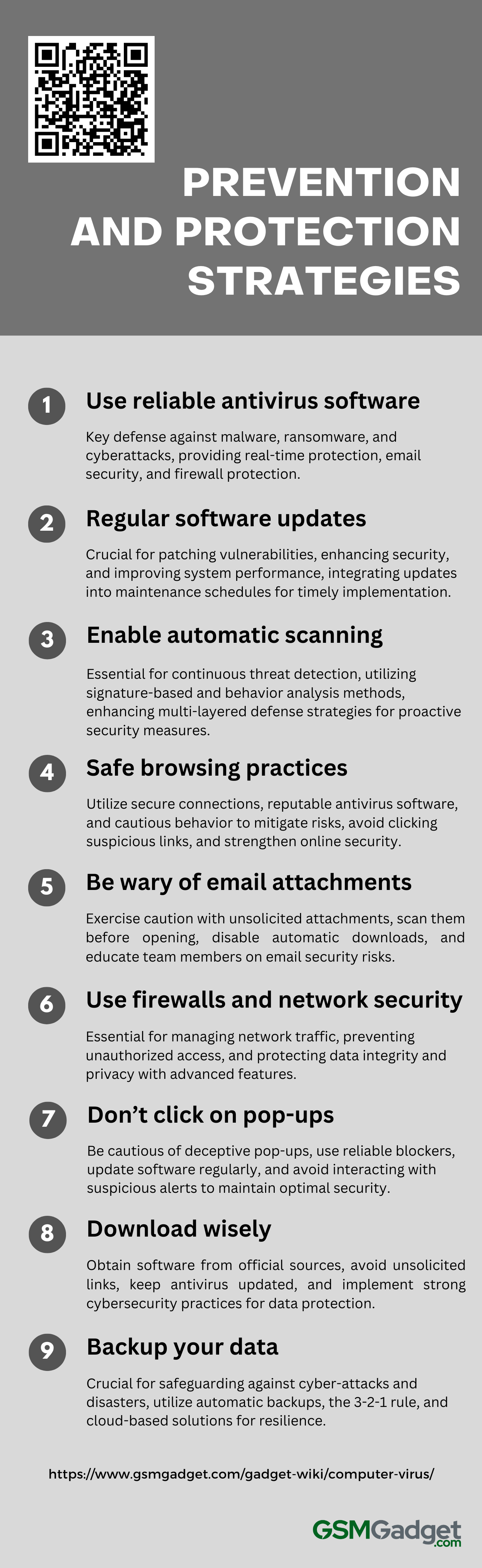
1. Use of reliable antivirus software
In the technology-driven world of digital security, reliable antivirus software is crucial for defending against a range of cyber threats, such as malware, ransomware, and various cyberattacks. These advanced solutions continuously scan and monitor systems, utilizing both signature-based and heuristic-based detection methods to identify and neutralize both known and unknown threats, ensuring real-time protection and system integrity. With features like email security, spam blocking, and firewall protection, antivirus programs not only eliminate potential threats but also prevent unauthorized access, thereby safeguarding sensitive data and ensuring operational continuity. While no solution can provide complete immunity, particularly against zero-day exploits, regularly updated antivirus software, as part of a multi-layered security approach, plays a key role in reducing the risk of infection and lessening the impact of cyberattacks.
2. Regular software and system updates
In the field of cybersecurity, it is crucial to regularly update software and systems in order to stay ahead of potential threats. These updates often include critical patches that address newly discovered vulnerabilities, preventing cybercriminals from exploiting these weaknesses to launch attacks. Keeping software and operating systems up to date not only enhances security measures but also improves system performance and stability. It is recommended that organizations and individuals integrate update procedures into their maintenance schedules and automate the process for timely implementation. This practice is essential for protecting digital infrastructure against evolving cyber risks, decreasing the risk of data breaches, and maintaining a strong security posture.
3. Enable automatic scanning
In the current digital environment, the implementation of automatic scanning is a crucial strategy for continuously safeguarding systems against malicious threats. This approach involves configuring security software to conduct regular scans to detect malware, viruses, and other cyber threats without manual intervention. This helps reduce the risk of oversight and limits opportunities for attackers. Automatic scanning utilizes signature-based methods, heuristics, and behavior analysis to identify both known and emerging threats, playing a significant role in a comprehensive multi-layered defense strategy. Tools such as those offered by Astra Security enhance this process by providing real-time threat detection and systematic scanning of network environments and applications, enabling prompt identification and resolution of vulnerabilities to maintain proactive security measures. This not only strengthens the protection of sensitive data and systems but also aids in meeting regulatory requirements, safeguarding the organization’s reputation, and ensuring operational continuity.
4. Safe browsing practices
In the digital age, it is essential to practice safe browsing habits to protect personal and corporate data from cyber threats. Utilizing a combination of prevention and protection strategies, such as using updated browsers with secure connections (HTTPS), enabling firewalls, and installing reputable antivirus software, can significantly decrease the risk of malicious attacks. It is important to remain vigilant by avoiding clicking on suspicious links, downloading from untrusted sources, and being cautious with personal information online. Strengthening security measures by using strong, unique passwords, changing them regularly, and implementing multi-factor authentication can further enhance protection. Tools like Google’s Safe Browsing can check URLs against known threats, while regularly clearing cookies and cache can help maintain privacy. By staying informed about the latest phishing techniques and incorporating these practices, individuals and organizations can confidently navigate the internet, shielded from both current and emerging online vulnerabilities.
5. Be wary of email attachments
In the realm of cybersecurity, email attachments stand as a prevalent conduit for threats such as malware, ransomware, and phishing attacks. Vigilance is paramount; users must exercise caution with attachments, even those from seemingly trusted sources. It is imperative to scan all attachments with up-to-date antivirus software prior to opening, as they may contain malicious code aimed at compromising your system. Be particularly wary of unsolicited attachments, verify the sender’s authenticity when in doubt, and assess the attachment’s pertinence to your ongoing communications. To enhance security measures, consider disabling automatic downloads in your email settings, be cautious of unusual file extensions, and avoid enabling macros, which cybercriminals exploit to trigger malicious activities on your device. The integration of robust email filtering solutions and the education of team members on the potential dangers of email attachments are also key strategies in fortifying your defenses against these insidious cyber risks.
6. Use of firewalls and network security
In the cybersecurity landscape, firewalls are crucial as they act as sentinels, managing network traffic to thwart unauthorized access and external threats. They are a blend of hardware and software that enforce security rules, allowing safe communication while preventing potential breaches. Network security is bolstered by tools like intrusion detection systems, encryption, and secure socket layers, which protect data integrity and privacy. Advanced firewalls, such as Next-Generation Firewalls, incorporate features like Intrusion Prevention Systems and Deep Packet Inspection, elevating their capability to detect and neutralize complex attacks. For optimal effectiveness, it’s vital to configure firewalls meticulously, update them regularly, and maintain vigilant monitoring to counter the dynamic nature of cyber threats, thus ensuring the security of network resources.
7. Don’t click on pop-ups
In the informative and technical field of cybersecurity, it is crucial to be cautious of pop-ups that may appear as legitimate alerts or attractive deals but could potentially serve as entry points for malware, spyware, or phishing attacks that pose a threat to the security of your personal data and system integrity. To protect against these risks, it is recommended to use reliable pop-up blockers and ensure that your antivirus software is regularly updated to provide proactive defense. It is also important to regularly update your browser and operating system to defend against new threats. If you come across a pop-up, it is advised to refrain from clicking on it, as even seemingly harmless interactions can result in security breaches. It is essential to verify the legitimacy of any pop-up and close it using the functions of your browser to maintain optimal security. Remember, exercising caution for a brief moment can prevent numerous security issues.
8. Download wisely
In the digital age, downloading software or content requires vigilance to protect against security risks that threaten personal and professional data. It’s essential to download files only from official websites and reputable app stores to avoid malware and phishing attacks. Keeping antivirus software updated and set to scan downloads automatically is a key defense. Caution is advised against unsolicited download links and offers that seem too good to be true, as they may harbor malicious intent. A proactive cybersecurity approach includes regular updates of all software, strong password policies, multi-factor authentication, and continuous monitoring of network traffic and user activity. These practices, alongside using applications like Wisely that offer transaction alerts and direct deposit setups, form a comprehensive strategy to reduce the risk of unauthorized access and maintain the integrity of your digital ecosystem.
9. Backup your data
In the digital age, it is essential to safeguard data to protect against threats such as cyber-attacks, hardware failures, and natural disasters. A comprehensive backup strategy is crucial, which includes regular, automatic backups to secure locations like cloud storage or external hard drives. Utilizing a combination of full, incremental, and differential backup methods is important. The 3-2-1 backup rule, which involves maintaining three copies of data on two different media, with one copy stored offsite, enhances data protection. It is important to periodically verify the integrity of backups and utilize modern cloud-based solutions for scalable and cost-effective data safety. Continuously testing and updating backup procedures helps to ensure resilience against evolving digital threats, enabling individuals and organizations to maintain operational continuity and protect valuable information.
Examples of Computer Virus
In the digital age, computer viruses have become a widespread threat to the security and efficiency of technology-driven lives. These malicious programs can cause havoc on personal and corporate systems, leading to data loss, theft, and widespread disruption. In the following section, we will examine several well-known computer viruses that have had significant impacts over the years.
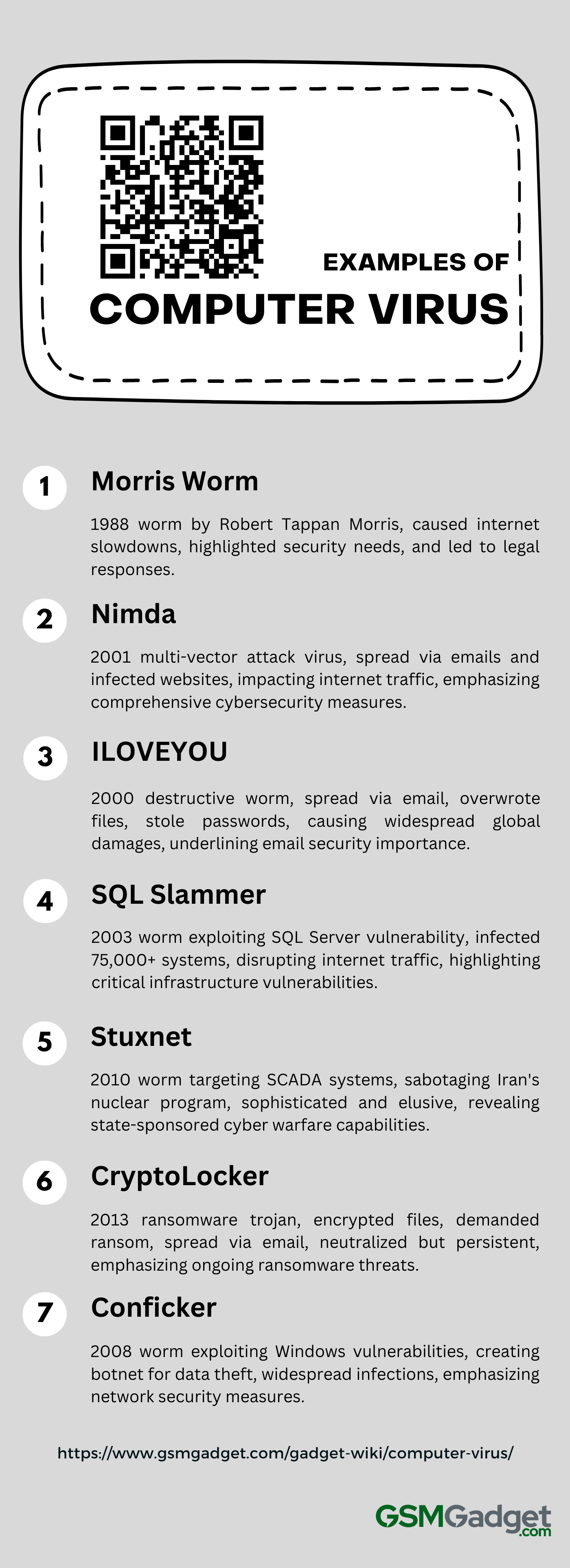
1. Morris Worm
The Morris Worm, created by Robert Tappan Morris in 1988, is a well-known early example of a computer worm that caused significant disruption due to a programming error that resulted in its excessive replication. Originally intended to gauge the size of the internet, it unintentionally exploited vulnerabilities in the UNIX operating system, specifically in the fingerd and sendmail processes, allowing it to spread independently and infect approximately 10% of the 60,000 internet-connected computers, including prominent universities and government facilities. The worm’s replication led to substantial slowdowns and system crashes, impacting about 6,000 machines and highlighting the need for strong cyber-security measures. The aftermath of this incident prompted the formation of the first Computer Emergency Response Team (CERT) and led to the first conviction under the 1986 Computer Fraud and Abuse Act, representing a significant milestone in the development of legal responses to cybercrimes.
2. Nimda
The Nimda virus, discovered in 2001, represented a multi-vector attack malware that spread through emails, network vulnerabilities, infected websites, and file sharing in order to gain administrative access and disrupt systems. It significantly impacted internet traffic and system performance by infecting servers and personal computers. Its capability to self-propagate through mass-mailing further extended its reach. This malware, which targeted system administrators, underscored the importance of implementing comprehensive cybersecurity measures, a lesson that continues to be relevant.
3. ILOVEYOU
The ILOVEYOU virus, also known as LoveLetter or the Love Bug, was a destructive computer worm that emerged in 2000 and caused widespread damage by tricking users into opening an email attachment disguised as a love letter. Upon activation, it would overwrite files, steal passwords, and spread by sending itself to the victim’s email contacts, leading to an estimated $10 billion in damages globally.
4. SQL Slammer
SQL Slammer, also known as Sapphire, appeared as a well-known computer worm in 2003 by exploiting a buffer overflow vulnerability in Microsoft SQL Server 2000. It infected over 75,000 systems almost immediately and caused significant disruptions. Its rapid spread led to a global slowdown of internet traffic and impacted critical services such as financial systems and air travel.
5. Stuxnet
Discovered in 2010, Stuxnet is a highly sophisticated computer worm developed by U.S. and Israeli intelligence agencies to target SCADA systems, specifically Iran’s nuclear program. It exploits zero-day vulnerabilities in Windows and manipulates industrial control systems to sabotage uranium enrichment centrifuges, all while avoiding detection by monitoring systems.
6. CryptoLocker
CryptoLocker, a ransomware trojan that surfaced in 2013, notoriously encrypted Windows users’ files and demanded a ransom for the decryption keys. It propagated via infected email attachments, employing robust encryption protocols that left victims’ files inaccessible without the keys, and although neutralized by Operation Tovar, its influence endures through various iterations, highlighting the persistent risk of ransomware.
7. Conficker
Conficker, also known as Downup, Downadup, or Kido, is a computer worm that is notorious for exploiting vulnerabilities in Microsoft Windows in order to spread through network shares and removable media. First discovered in 2008, this worm has infected millions of computers, creating a botnet for stealing data and spreading additional malware, causing major security issues worldwide.
How to Remove a Computer Virus
To remove a computer virus, you can follow these general steps:
- Enter Safe Mode: To initiate the process, restart your computer and access Safe Mode, typically done on Windows by pressing F8 during startup.
- Delete Temporary Files: Use the Disk Cleanup utility to remove temporary files that may harbor viruses.
- Run a Virus Scan: Perform a comprehensive scan using your antivirus software, or install a trusted one if you do not already have it.
- Address Detected Threats: Follow the prompts from your antivirus software to remove or quarantine any detected malware.
- Update Your Software: Ensure that your operating system and all applications are updated with the latest security patches.
- Secure Your Accounts and Data: After completing the cleanup process, it is recommended to change your passwords to enhance the security of your accounts. Additionally, it is important to regularly back up your data in order to protect against potential future threats. If the virus continues to persist, consider using specialized tools such as Microsoft’s Malicious Software Removal Tool for manual removal, or seek professional assistance if needed.
